
Trust Center Due Diligence: What 404 Software Companies Reveal About Compliance
This article is written for acquirers of Lower-Middle-Market (LMM) software companies—including Private Equity buyers, holding companies, and strategic acquirers.
TL;DR
It has become standard and expected for B2B software companies to have a Trust Center to showcase their compliance achievements. Expect it and proceed with skepticism if there isn't one.
- Third-Party Provider: In our search for Trust Center pages containing compliance badges, 98.5% (398/404) of the pages we found were "Powered By" third party providers. When diligencing a B2B software company, you should expect a Trust Center that is professionally "Powered By" a credible provider — if you don't see that, it should trigger a variety of follow-up questions.
- Standardization: The vast majority (95% - 382/404) of the Trust Center pages we reviewed, included at least one "badge" for a well-known standard (e.g. SOC 2, ISO 27001, etc). When diligencing a B2B software company, you should expect one or more industry-standard compliance badges, not just a list of bespoke controls implemented by the company. We also saw at least 20 badge types that we never saw on any other Trust Center page in the dataset. When you see a compliance badge with a logo or caption you've never seen before, approach with skepticism whether it signals anything materially relevant about the target's compliance program.
- Open-to-the-Public: On our way to studying over four-hundred Trust Center pages that proudly showcase the host company's compliance achievements, there were 57 others that we couldn't include because they were auth-gated, although the authentication page made it very clear that what was behind the auth page was going to be a Trust Center. So, of 461 Trust Center pages we would have liked to study, we put all of our focus on the 88% (404/461) that were open for viewing. Clearly, as someone diligencing an acquisition target, you should ask for — access to any auth-gated trust center, and be given — access just as clients/prospects get. In fact, we view that as superior source of truth relative to whatever the target might populate a data room with.
Breadth of Compliance Programs
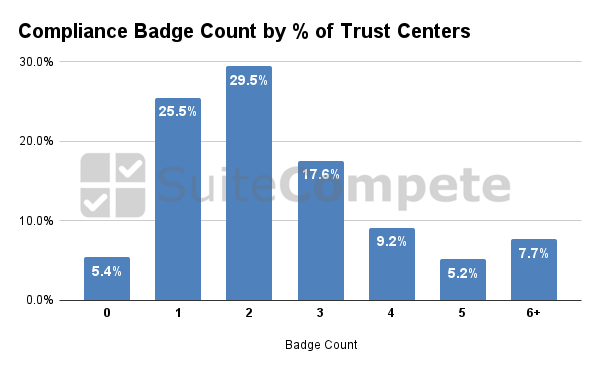
We were interested in taking a deep dive to understand trends in the number of compliance badges shown on Trust Center pages. You wouldn't be surprised to see a B2B Software company with a Trust Center page featuring a SOC 2 compliance badge — it's hard for a U.S.-focused software company to win middle-market and enterprise customers without it. But, how much deeper have companies trended to go, into standards compliance? Here's a look at the percentage of Trust Center pages that had zero (yes, zero) badges, one badge, two badges, etc:
Brief thoughts:
- Zero Badges? We did a double-take. Yes, 5% of Trust Center pages we saw, showed zero compliance badges. What in the world did they show, you ask? Typically, a less-than-compelling laundry list of controls. For example, a page that lists controls related to Data Backups, Encryption-at-Rest, Encryption-in-Transit, Multi-Factor Authentication. We suspect that organizations showcasing a laundry list of controls but not (yet?) badges of standardized compliance (e.g. SOC 2) will uncover significant holes in their compliance program when (if) they progress with standards compliance.
- The Median: In a data point that is likely a significant help to acquirers of software companies, the median Trust Center in the dataset had two compliance badges (most frequent combo: SOC 2 + ISO 27001). The more a target has compliance with well-defined standards, the bigger a due diligence head start an acquirer has in understanding the target's compliance program.
- The (Positive) Outliers: 39.6% (160/404) had three or more compliance badges. Great. And, more specifically, 22.0% (89/404) had four or more compliance badges. Imagine getting into due diligence and seeing substantive, third-party-validated evidence of (for example) SOC 2, ISO 27001, GDPR, and PCI DSS. Compare that to how you'd feel in the "Zero Badges" due diligence situation.
You now have hard data about the current norms regarding the breadth of compliance programs that B2B software companies claim on their Trust Centers.
The Most Popular Compliance Badges
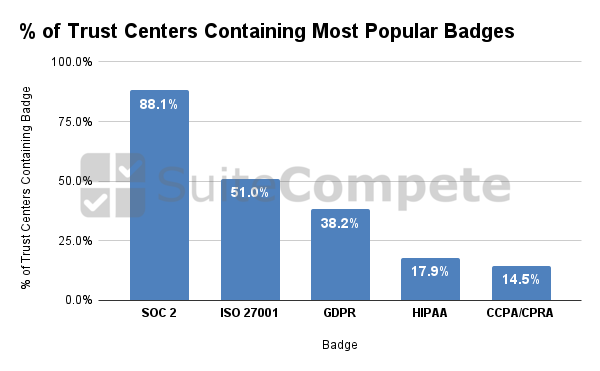
If you are an acquirer of B2B software companies with portfolio companies that have a presence in the U.S., and sometimes some international customers, you likely won't be surprised by our data around the two most popular compliance badges (but keep reading for some eye-openers as we get into the details). Here are the most popular:
Our take:
- SOC 2 is the Obvious Baseline: If you diligence software companies, especially ones with any significant U.S. customer base, you already know this. But, just to be incredibly clear: if you are diligencing a B2B software acquisition target that lacks SOC 2, that should be just as alarming to you as if they lacked a professionally "Powered By" Trust Center.
- SOC 2 / ISO 27001 for U.S. + International: Companies serving a mix of U.S.-based and Internationally-based customers, seem to be getting good value out of that particular combination of compliance claims, with our belief being that the driver of ISO 27001 requests is likely skewed slightly towards requests from customers whose presence spans beyond the U.S.
- CCPA/CPRA: This one was a bit of a surprise to us. Not because it is unimportant. But, we didn't necessarily expect it to be in the top five. What we're hearing? Companies that have already navigated GDPR, already have many of the practices in place that support a CCPA/CPRA program. That headstart may be accelerating the pace of CCPA/CPRA compliance, relative to the pace that B2B software companies would acclimate to a new compliance obligation without the "headstart" from another popular compliance program with significant overlap in requirements.
Suprises:
- PCI DSS: NOT shown on the chart of the top five compliance badges, is PCI DSS. In fact, of the Trust Center pages we reviewed, only 8.1% showed a PCI DSS badge. It would be hard to believe (as just one example), that only 8.1% of the sample set have some type of self-service credit card checkout on their site. Are B2B software companies parsing the PCI DSS documentation in some especially narrow manner that has them omitting PCI DSS from their compliance priorities? We feel confident that a higher percentage than 8.1% have some PCI DSS obligation, whether they know it or not.
- WCAG: We aren't surprised that WCAG didn't crack the top five, but we were surprised how far down the list it was. It was the ninth most popular compliance badge to be seen in Trust Centers, appearing in only 4.2% of the ones in this study. There is reasonably broad publicly availability tooling to assist with WCAG compliance, and we had expected it to be more prominent in the "top badges" analysis. Our current hypothesis is that there may be more companies in the dataset that have WCAG compliance, who simply did not think to include it in their Trust Center compliance badges.
Correlation as a Preview
We alluded to this in the prior section, but there are certain compliance programs that seem to travel in pairs. Through a correlation analysis that we conducted on this dataset, here are some of the compliance programs that are often seen together on the same Trust Center:
- ISO 27017 and ISO 27018: we think of the former as being general cloud security focused, and the latter as being focused on Personally Identifiable Information (PII) cloud security. If an acquisition target has one but not the other, it would be worth asking to understand if there is some intentionality in their approach.
- SOC 2 and ISO 27001: we've covered this a bit, above. We see this as an wise choice for B2B software companies that have a mix of U.S.-based and international clients. We'd be pleased to see acquisition targets with this combination of compliance badges; it's a great starting point.
- ISO 27001 and GDPR: if an acquisition target has ISO 27001, we suspect that the "origin story" was a non-U.S. based client/prospect urging them to do so. If one or more of those international clients are EU-based, we'd be surprised if the acquisition target didn't have an obligation to comply to GDPR as well. We'd hope to see a GDPR compliance badge for most situations where a company has ISO 27001, unless the driver of ISO 27001 was something other than an EU presence. And, in practice in the data, these two compliance badges are definitely correlated.
- HITRUST and NIST CSF: the data set shows correlation between the presence of these two, and we aren't surprised. A good read if you want to understand why these are correlated, is the HITRUST “Companion Guide for NIST 2.0.”
We have more to say about correlation of various compliance badges, in future posts.
Wrapping Up
We have much more to say on this topic, and feel free to reach out if you would like to work together commercially on any diligence efforts related to compliance or beyond.
